棧緩衝區溢出
此條目目前正依照其他維基百科上的內容進行翻譯。 (2024年7月17日) |
棧緩衝區溢出(stack buffer overflow或stack buffer overrun)是電腦程式把數據寫入調用棧上的內存時超出了資料結構的邊界。[1][2]棧緩衝區溢出是緩衝區溢出的一種。[1] 這會損壞相鄰數據的值,引發程序崩潰或者修改了函數返回地址從而導致執行惡意的程序。這種攻擊方式稱為stack smashing。可被用於注入可執行代碼、接管進程的執行。是最為古老的黑客攻擊行為之一。[3][4][5]
例子
[編輯]下例可用於覆蓋函數返回地址。[3][6] 通過函數 strcpy() :
#include <string.h>
void foo (char *bar)
{
char c[12];
strcpy(c, bar); // no bounds checking
}
int main (int argc, char **argv)
{
foo(argv[1]);
return 0;
}
當命令行參數少於12個字符時(例子B時)該程序是安全的。
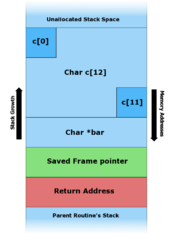
foo()函數的不同輸入下的調用棧,下圖展示32位元小端序(little-endian)系統發生棧緩衝區溢出的記憶體狀態:
 |
 |
 |
例子C中, 命令行參數多於11個字符,導致foo()覆蓋了本地調用棧的數據、存儲的棧指針(EBP)以及最重要的返回地址。
攻擊也可以修改內部變量值:
#include <string.h>
#include <stdio.h>
void foo (char *bar)
{
float My_Float = 10.5; // Addr = 0x0023FF4C
char c[28]; // Addr = 0x0023FF30
// Will print 10.500000
printf("My Float value = %f\n", My_Float);
/* ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Memory map:
@ : c allocated memory
# : My_Float allocated memory
*c *My_Float
0x0023FF30 0x0023FF4C
| |
@@@@@@@@@@@@@@@@@@@@@@@@@@@@#####
foo("my string is too long !!!!! XXXXX");
memcpy will put 0x1010C042 (little endian) in My_Float value.
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~*/
memcpy(c, bar, strlen(bar)); // no bounds checking...
// Will print 96.031372
printf("My Float value = %f\n", My_Float);
}
int main (int argc, char **argv)
{
foo("my string is too long !!!!! \x10\x10\xc0\x42");
return 0;
}
平台相關
[編輯]A number of platforms have subtle differences in their implementation of the call stack that can affect the way a stack buffer overflow exploit will work. Some machine architectures store the top level return address of the call stack in a register. This means that any overwritten return address will not be used until a later unwinding of the call stack. Another example of a machine specific detail that can affect the choice of exploitation techniques is the fact that most RISC style machine architectures will not allow unaligned access to memory.[7] Combined with a fixed length for machine opcodes this machine limitation can make the jump to ESP technique almost impossible to implement (with the one exception being when the program actually contains the unlikely code to explicitly jump to the stack register).[8][9]
Stacks that grow up
[編輯]Within the topic of stack buffer overflows, an often discussed but rarely seen architecture is one in which the stack grows in the opposite direction. This change in architecture is frequently suggested as a solution to the stack buffer overflow problem because any overflow of a stack buffer that occurs within the same stack frame can not overwrite the return pointer. Further investigation of this claimed protection finds it to be a naive solution at best. Any overflow that occurs in a buffer from a previous stack frame will still overwrite a return pointer and allow for malicious exploitation of the bug.[10] For instance, in the example above, the return pointer for foo will not be overwritten because the overflow actually occurs within the stack frame for strcpy. However, because the buffer that overflows during the call to strcpy resides in a previous stack frame, the return pointer for strcpy will have a numerically higher memory address than the buffer. This means that instead of the return pointer for foo being overwritten, the return pointer for strcpy will be overwritten. At most this means that growing the stack in the opposite direction will change some details of how stack buffer overflows are exploitable, but it will not reduce significantly the number of exploitable bugs.
保護方式
[編輯]常用三種方式來對抗棧緩衝區溢出攻擊。
檢查棧緩衝區溢出的發生
[編輯]棧的警惕標誌(stack canary),得名於煤礦里的金絲雀,用於探測該災難的發生。具體辦法是在棧的返回地址的存儲位置之前放置一個整形值,該值在裝入程序時隨機確定。棧緩衝區攻擊時從低地址向高地址覆蓋棧空間,因此會在覆蓋返回地址之前就覆蓋了警惕標誌。返回返回前會檢查該警惕標誌是否被篡改。[2]
棧數據不可執行
[編輯]採取了「寫異或執行」策略(W^X, "Write XOR Execute"),即內存要麼可寫,要麼可執行,但二者不能兼得。這是最常用的方法,大部分桌面處理器都硬體支持不可執行標誌(no-execute flag)。
While this method definitely makes the canonical approach to stack buffer overflow exploitation fail, it is not without its problems. First, it is common to find ways to store shellcode in unprotected memory regions like the heap, and so very little need change in the way of exploitation.[11]
Even if this were not so, there are other ways. The most damning is the so-called return to libc method for shellcode creation. In this attack the malicious payload will load the stack not with shellcode, but with a proper call stack so that execution is vectored to a chain of standard library calls, usually with the effect of disabling memory execute protections and allowing shellcode to run as normal.[12] This works because the execution never actually vectors to the stack itself.
A variant of return-to-libc is return-oriented programming, which sets up a series of return addresses, each of which executes a small sequence of cherry-picked machine instructions within the existing program code or system libraries, sequence which ends with a return. These so-called gadgets each accomplish some simple register manipulation or similar execution before returning, and stringing them together achieves the attacker's ends. It is even possible to use "returnless" return-oriented programming by exploiting instructions or groups of instructions that behave much like a return instruction.[13]
隨機化內存空間布局
[編輯]Instead of separating the code from the data another mitigation technique is to introduce randomization to the memory space of the executing program. Since the attacker needs to determine where executable code that can be used resides, either an executable payload is provided (with an executable stack) or one is constructed using code reuse such as in ret2libc or ROP (Return Oriented Programming) randomizing the memory layout will as a concept prevent the attacker from knowing where any code is. However implementations typically will not randomize everything, usually the executable itself is loaded at a fixed address and hence even when ASLR (Address Space Layout Randomization) is combined with a nonexecutable stack the attacker can use this fixed region of memory. Therefore all programs should be compiled with PIE (position-independent executables) such that even this region of memory is randomized. The entropy of the randomization is different from implementation to implementation and a low enough entropy can in itself be a problem in terms of brute forcing the memory space that is randomized.
隨機化內存空間布局(ASLR)會對處理程序的記憶體區段地址進行隨機化,阻止攻擊者進行返回導向編程與跳至Shellcode的攻擊手法,因為攻擊者需要知道可執行區段與 Shellcode 的記憶體地址。執行檔如果不是地址無關代碼(PIE)的格式,會導致執行檔載入成處理程序之後,部分區段地址為固定的(如 .text 區段),攻擊者在Linux系統上,依然可以 return 到 0x400000 地址。ASLR受到資訊熵的影響,不同的實作會有不同的資訊熵,過低的資訊熵使攻擊者更容易猜測到地址,也因此32位元比起64位元的更容易受到威脅。也因此在2015年發生Stagefright漏洞,在32位元系統下,ASLR僅有8位元的資訊熵,因此每次漏洞利用,只需要從256種組合猜測可能的記憶體地址進行利用[14]。
著名例子
[編輯]- 莫里斯蠕蟲針對Unix finger 伺服器.[1] (頁面存檔備份,存於網際網路檔案館)
- Witty worm .[2]
- Slammer worm針對Microsoft SQL Server.[3] (頁面存檔備份,存於網際網路檔案館)
- 衝擊波蠕蟲 針對微軟的DCOM 服務.
- Twilight hack針對Wii
參見
[編輯]參考文獻
[編輯]- ^ 1.0 1.1 Fithen, William L.; Seacord, Robert. VT-MB. Violation of Memory Bounds. US CERT. 2007-03-27 [2017-02-19]. (原始內容存檔於2012-02-05).
- ^ 2.0 2.1 Dowd, Mark; McDonald, John; Schuh, Justin. The Art Of Software Security Assessment. Addison Wesley. November 2006: 169–196. ISBN 0-321-44442-6.
- ^ 3.0 3.1 Levy, Elias. Smashing The Stack for Fun and Profit. Phrack. 1996-11-08, 7 (49): 14 [2017-02-19]. (原始內容存檔於2021-03-04).
- ^ Pincus, J.; Baker, B. Beyond Stack Smashing: Recent Advances in Exploiting Buffer Overruns (PDF). IEEE Security and Privacy Magazine. July–August 2004, 2 (4): 20–27 [2017-02-19]. doi:10.1109/MSP.2004.36. (原始內容存檔 (PDF)於2016-03-04).
- ^ Burebista. Stack Overflows (PDF). [2017-02-19]. (原始內容 (PDF)存檔於2007-09-28). (dead link)
- ^ Bertrand, Louis. OpenBSD: Fix the Bugs, Secure the System. MUSESS '02: McMaster University Software Engineering Symposium. 2002 [2017-02-19]. (原始內容存檔於2007-09-30).
- ^ pr1. Exploiting SPARC Buffer Overflow vulnerabilities. [2017-02-19]. (原始內容存檔於2012-02-05).
- ^ Curious. Reverse engineering - PowerPC Cracking on Mac OS X with GDB. Phrack. 2005-01-08, 11 (63): 16 [2017-02-19]. (原始內容存檔於2013-10-05).
- ^ Sovarel, Ana Nora; Evans, David; Paul, Nathanael. Where’s the FEEB? The Effectiveness of Instruction Set Randomization. [2017-02-19]. (原始內容存檔於2024-07-17).
- ^ Zhodiac. HP-UX (PA-RISC 1.1) Overflows. Phrack. 2001-12-28, 11 (58): 11 [2017-02-19]. (原始內容存檔於2013-12-02).
- ^ Foster, James C.; Osipov, Vitaly; Bhalla, Nish; Heinen, Niels. Buffer Overflow Attacks: Detect, Exploit, Prevent (PDF). United States of America: Syngress Publishing, Inc. 2005 [2017-02-19]. ISBN 1-932266-67-4. (原始內容存檔 (PDF)於2023-12-26).
- ^ Nergal. The advanced return-into-lib(c) exploits: PaX case study. Phrack. 2001-12-28, 11 (58): 4 [2017-02-19]. (原始內容存檔於2014-01-27).
- ^ Checkoway, S.; Davi, L.; Dmitrienko, A.; Sadeghi, A. R.; Shacham, H.; Winandy, M. Return-Oriented Programming without Returns. Proceedings of the 17th ACM conference on Computer and communications security - CCS '10. October 2010: 559–572. ISBN 978-1-4503-0245-6. doi:10.1145/1866307.1866370.
- ^ Mark Brand. Stagefrightened?. Project Zero. Google.
